From the
OpenBSD Journal and the
release page :
As you can now easily tell from the OpenBSD main web site, OpenBSD 5.5 has been released.
Looking at the
release announcement and other sources such as the
release page , it's easy to see that there are numerous goodies in store for you:
- A whole new traffic shaping system to replace ALTQ
- Cryptographically signed base sets and packages
- Automatic installation features
- Improved hardware support, and more
Also, from OpenBSD 5.5 onwards, OpenBSD is year 2038 ready and will run well beyond Tue Jan 19 03:14:07 2038 UTC. The entire source tree (kernel, libraries, and userland programs) has been carefully and comprehensively audited to support 64-bit time_t.
 Phys.org reports
Phys.org reports :
A robotic space plane is speeding in low Earth orbit at this very moment. Some say it's a weapon; others, a data-gathering mission. There's one fact most agree on as the plane hits 500 days in space: Its real purpose is a mystery.
The Boeing-built X-37B Orbital Space Vehicle, constructed in California, is one-fourth the size of the Endeavour Space Shuttle.
Whatever its real purpose, the X-37B has very real capabilities. It travels low in orbit, staying around 110 to 500 miles above the Earth at a cruising speed of about 17,500 mph. It's equipped with special heat-shield tiles for re-entry, which are billed by Boeing as tougher than Endeavour's.
But the government's treatment of the project poses questions. Though it's advertised as a secret project, Boeing releases pictures and more than two pages of details on the X-37B. In contrast, the secret, super-fast Lockheed SR-71 Blackbird was not declassified until decades after it had been used in the Vietnam War.
More pictures and speculation can be found at
Extremetech .
A very recent
firmware analysis from the reverse engineer Eloi Vanderbeken shows that NETGEAR didn't fix the backdoor on port 32764 but instead implemented a knocking feature that is now required to unlock the service.
Summary from the slides: The knocking feature is initiated when a "packet type == 0x201" arrived at "ft_tool" that listens to the Ethernet packets. It only works with EtherType 0x8888 and the payload has to be "45d1bb339b07a6618b2114dbc0d7783e" which is the MD5-hash of the model number DGN1000. If such a packet arrives, the backdoor service /usr/bin/scfgmgr f- is launched.
Ars Technica reports :
The nature of the change, which leverages the same code as was used in the old firmware to provide administrative access over the concealed port, suggests that the backdoor is an intentional feature of the firmware and not just a mistake made in coding. "It's DELIBERATE," Vanderbecken asserted in his presentation.
(Cross posted on Soylentnews)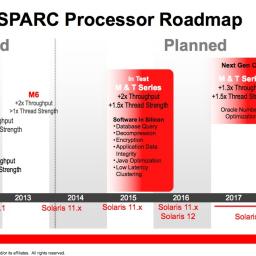
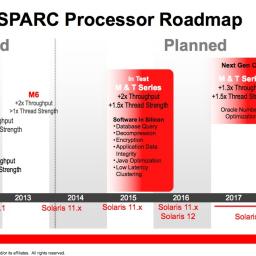
Oracle has published a
roadmap [PDF] for its SPARC and Solaris platforms and makes a commitment to SPARC until at least 2019. This was picked up by The Register in a recent
article :
Optimists will be pleased that Oracle appears to have three generations of silicon in mind and appears committed to SPARC until 2019 and beyond. Pessimists might wonder if the "core enhancements" due around 2019 represent a worryingly vague statement of direction and/or intent. The planned 2017 and 2018 enhancements to thread strength and throughput also look incremental compared to the heftier enhancements planned for 2015 and 2016, which could be worrying for those who need SPARC to scale.
[Cross-posted at SoylentNews.org]
Germany's Angela Merkel isn't the only one riled over recent revelations of American surveillance and data gathering. Turns out
The American government conducted a major intelligence offensive against China , with targets including the Chinese government and networking company Huawei.
Edward Snowden is the source of the revelations, as reported to German daily Spiegel. Among the American intelligence service's targets were former Chinese President Hu Jintao, the Chinese Trade Ministry, banks, as well as telecommunications companies. But the NSA made a special effort to target Huawei.
According to a top secret NSA presentation, NSA workers not only succeeded in accessing the email archive, but also the secret source code of individual Huwaei products."